HTTPS Certificate
ACMEMGR.SH is an ACME.SH manager for unlimited CERTS, TLS services, hosts and DNS-01 accounts from domains names providers.
ACMEMGR.SH is designed to go hand in hand with ACME.SH, the most valuable V1 and V2 protocol compliant ACME client ever written for https://letsencrypt.org, the sole free, automated, and open certificate authority brought to you by the non-profit Internet Security Research Group (ISRG).
Like its companion and model ACME.SH, ACMEMGR.SH is “written purely in Shell (Unix shell) language” as pointed out by Neilpang the author of ACME.SH : no dependency at all (as we can’t seriously consider a shell script interpreter as a dependency in a Unix system).
ACMEMGR.SH manages :
- N domains certificates (through acme.sh and Let’s Encrypt);
- N https services (web, email, etc. – configurable childs scripts);
- N hosts (dedicated or virtual);
- N DNS-01 accounts (even from different hosting services).
Let’s Encrypt wildcard certificates can only be obtained through DNS-01 method as Let’s Encrypt considers it’s the only method that offers an adequate security level.
With ACMEMGR.SH, the management of hundreds of certificates, servers and other DNS-01 registrar accounts in a multi-account environment is simply handled by a single list in a single file.
The creation, deletion and renewal of certificates, as well as their propagation and deletion on remote servers, and email and service log dispatch, are managed transparently.
Features
- Handle wild certificates (like *.domain.tld)
- When creating certificate which starts with “www” (like “www.domain.tld”), it automatically adds the domain name “domain.tld” to the certificate
- Renewal certificate requests are only done when the current certificate is only valid for one month
- Certificate transactions (copy and delete) to remote host operations are fully customizable
- The certificate-linked service (Web, email, etc.) is only reloaded when the certificate is successfully created, renewed or deleted (only reloads when necessary)
- Moreover, the service is only restarted once, even if there is more than one updated certificate linked to the service (one reload only for N certificates, depending on the same service on the same host)
- Fully customizable service reload or restart after certificate update
- Defensive programming with consistent logging and emailing
- Extensive pre-checks remotely erase certificates marked for deletion. No use of recursive remove for safety reasons.
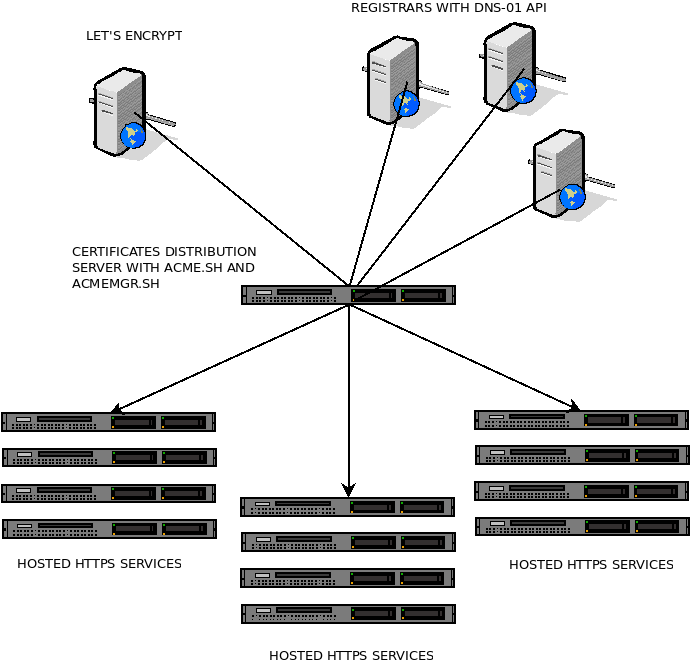
Architecture
The diagram at the top of the article is an overview of how it works. All the management is done in a centralized CERTIFICATE DISTRIBUTION SERVER :
- Only one host to manages a pool of registrars, hosts and domains names
- Simple, modulat and understandable architecture
- Only one file to manage : the domain name database.
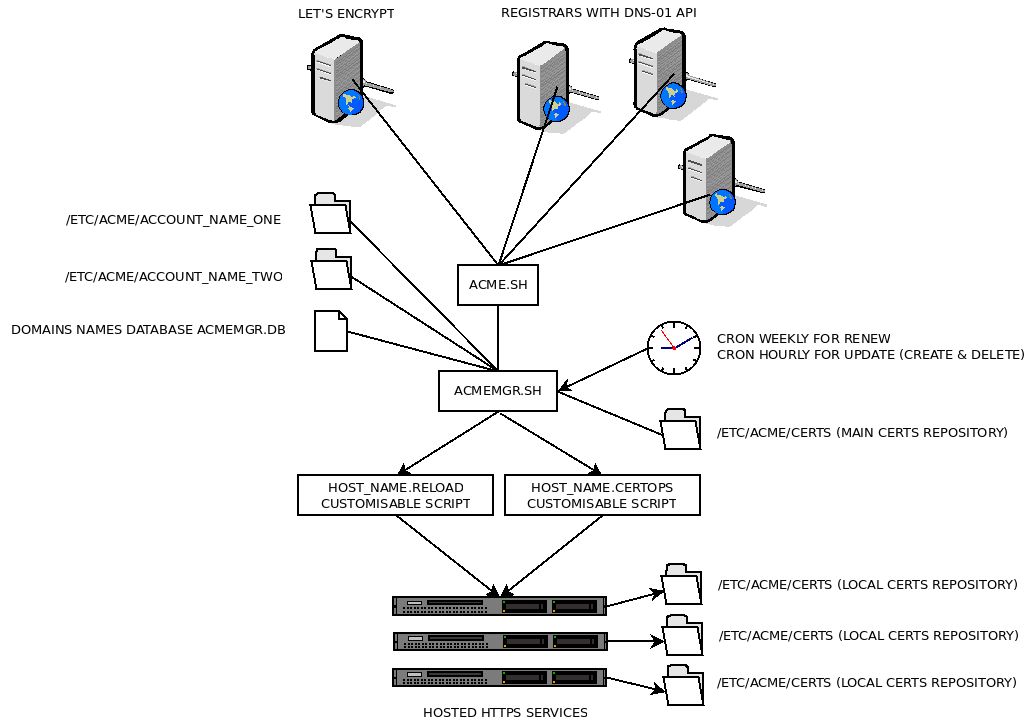
Below is a modular view how ACMEMGR.SH works. The CERTIFICATE DISTRIBUTION SERVER host only has:
- Two scripts : acme.sh and acmemgr.sh
- One database file, acmemgr.db, in a comma delimited text format
- One directory holding all certificates
- As many subdirectories as DNS-01 registrar accounts
- As many customizable scripts as needed to reload services and copy certificates.
Conclusion
ACMEMGR.SH has been extremely satisfactory for several years and contributors have made significant improvements.
The source and user’s manual are available on Github.
Sowebio plans to add more contributions to Libre software on its public repository.